
April 10, 2026
EnQuanta Research Team · 7 min read
Last week we published our analysis of the Lockheed Martin hack — the OSINT-driven doxxing of 28 defense engineers, the claimed 375 TB exfiltration, and what it all means for the harvest-now-decrypt-later threat facing the defense industrial base.
The question we’ve heard most since: How does something like this happen to Lockheed Martin?
The uncomfortable answer: CMMC compliance — the framework the entire defense industrial base is racing to adopt — wouldn’t have prevented it. Not the doxxing. Not the data exfiltration. Not the psychological operations that followed.
One of our advisors put it plainly: CMMC is not enough anymore. At EnQuanta, we have a phrase for the mindset that treats certification as protection: compliance is complacency.
This post breaks down what actually failed, what CMMC does and doesn’t cover, and what a defense-grade security posture actually looks like in 2026.
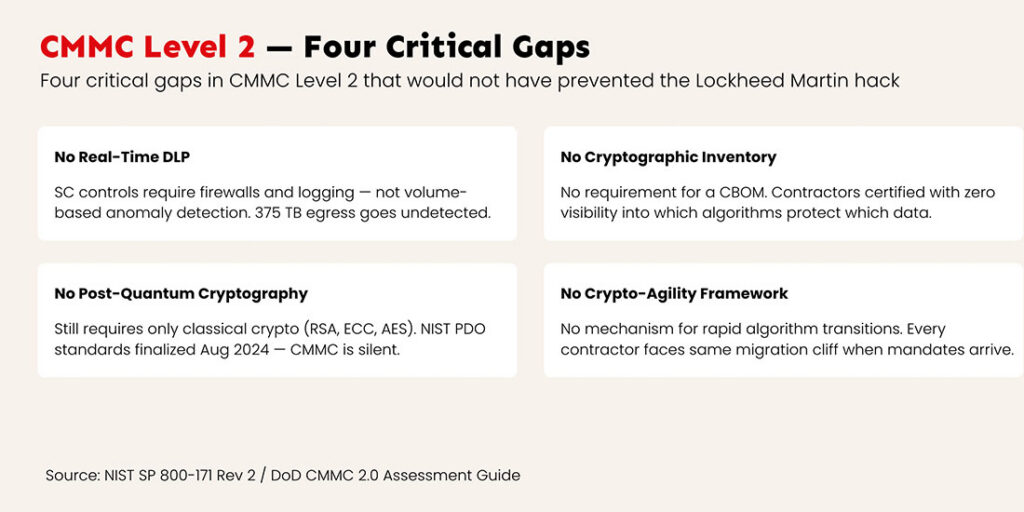
CMMC 2.0 Gaps: What the Framework Misses in 2026
CMMC 2.0 is built on NIST SP 800-171 — 110 security controls across 14 families. For Level 2, which covers most defense contractors handling Controlled Unclassified Information (CUI), the framework requires access controls, audit logging, incident response procedures, and encryption of CUI at rest and in transit.
On paper, it’s thorough. In practice, it has critical blind spots that the Lockheed Martin operation exposed.
No real-time data loss prevention mandate. CMMC’s System and Communications Protection (SC) controls require boundary protections and logging — firewalls, session monitoring, encrypted channels. What they don’t require is real-time anomaly detection on data volume. A compliant contractor can pass a CMMC Level 2 assessment while having zero capability to detect 375 terabytes of data leaving its network over days or weeks. Passive logging satisfies the control. Active exfiltration detection does not.
No cryptographic inventory requirement. CMMC requires encryption of CUI. It does not require organizations to maintain an inventory of what cryptographic algorithms protect which data assets, where those assets reside, or how those protections are configured across the enterprise. A contractor can be fully certified while having no idea which systems still run RSA-2048, which VPN tunnels use classical ECC, or where their most sensitive data actually lives.
No post-quantum cryptography guidance. CMMC 2.0 still references only classical cryptography — AES, RSA, ECC. NIST finalized its first post-quantum cryptography standards (FIPS 203, 204, 205) in August 2024. NSA’s CNSA 2.0 mandates quantum-resistant cryptography for all National Security System acquisitions by January 2027. CMMC is silent on both. Every compliant contractor is still running cryptography that’s vulnerable to harvest-now-decrypt-later collection — the exact threat model the Lockheed operation demonstrated.
No crypto-agility framework. Even when PQC mandates arrive, CMMC provides no mechanism for rapid cryptographic transitions. Crypto-agility — the ability to swap algorithms without rearchitecting systems — isn’t mentioned. This means every contractor faces the same migration cliff: when quantum mandates hit, they’ll be starting from zero.
The bottom line: a contractor can achieve CMMC Level 2 certification and still be fully exposed to the exact attack patterns Handala and APT Iran deployed against Lockheed Martin.
Lockheed Martin Breach Analysis: How 375 TB Leaves the Building
To understand what prevention actually looks like, we need to understand how these operations worked. The research points to two distinct but overlapping campaigns.
Credential-Based Initial Access: The Front Door Was Open
According to analysis from Check Point Research and Cybersecurity Dive, the likely initial access vector was compromised credentials — obtained through infostealer malware, previous data breaches, or password reuse. Handala’s established playbook (documented across the Stryker attack and other operations) relies on compromised VPN credentials, RDP-based lateral movement, and manual, hands-on operations that prioritize speed over stealth.
This is the most common initial access method in the defense sector — and the hardest to detect when multi-factor authentication isn’t enforced or when session anomaly detection isn’t deployed. CMMC requires MFA for remote access (Control 3.5.3), but enforcement gaps and legacy system exceptions are widespread.
OSINT Aggregation: The Data That Doesn’t Need to Be Stolen
The doxxing of 28 engineers was likely achieved through open-source intelligence aggregation, not a direct network breach. Nation-state actors combined social media profiles, public records, commercially available data, and previously compromised personal accounts to build targeting packages on individual engineers.
This is a threat vector CMMC doesn’t address at all — and honestly, it’s not one that any single cryptographic product solves either. We’re being upfront about that. OSINT-based targeting requires operational security training, personal data minimization, and security programs that extend beyond the enterprise perimeter to the individual. It’s a human problem that requires human solutions.
Mass Data Exfiltration: Where Technology Should Have Intervened
The 375 TB exfiltration claim — if accurate — represents a catastrophic failure of detection, not prevention. Exfiltrating that volume of data takes time, bandwidth, and sustained access. At typical enterprise egress speeds, moving 375 TB would require days to weeks of continuous large-scale data transfer.
Here’s where CMMC’s gaps become operational failures:
No volume-based anomaly detection. Standard SIEM and network monitoring tools can detect this — if they’re configured to alert on bulk data movement. CMMC doesn’t require it.
No data-at-rest movement monitoring. Standard SIEM tools can detect bulk data movement — if configured for it. CMMC doesn’t require this configuration. The gap between “logging exists” and “anomalies are detected” is where 375 TB disappears.
Defense Cybersecurity Beyond CMMC: What a Quantum-Ready Posture Looks Like
CMMC is a floor, not a ceiling. Passing a Level 2 assessment means you’ve met the minimum bar for handling CUI. It does not mean you can detect a sophisticated nation-state exfiltration operation, withstand harvest-now-decrypt-later collection, or respond to the kind of combined cyber-OSINT-psyops campaign that Handala executed.
Here’s what a quantum-ready, adversary-aware security posture adds on top of CMMC:
Post-Quantum Cryptography Migration: Close the HNDL Window
Every day that defense data sits behind RSA or ECC is another day of collection opportunity for adversaries running HNDL operations. QuantaCrypt’s dynamic-hybrid, crypto-agile framework eliminates the single-algorithm dependency that makes HNDL viable. No code rewrites; one set of library calls. The migration from multi-year roadmaps to manageable rollout cycles means the HNDL window starts closing immediately, not after a 3-year implementation.
Cryptographic Asset Visibility: Know What You’re Protecting
You can’t protect what you can’t see. Defense CISOs need a complete map of their cryptographic exposure surface — which algorithms protect which data, where vulnerabilities exist, and what needs to migrate first. This is the foundation for any PQC migration plan that moves faster than the adversary’s collection timeline.
Crypto-Agility: Stop Rearchitecting for Every Transition
CMMC will eventually require PQC. Then it will require whatever comes after PQC. Organizations that build for a single algorithm transition will face the same migration cliff every time standards evolve. Crypto-agility — the ability to swap cryptographic algorithms without rearchitecting infrastructure — is what turns a one-time scramble into an operational capability.
Our Take: The Lockheed Martin hack didn’t exploit exotic zero-days or novel attack techniques. It exploited the gap between what compliance frameworks require and what adversaries actually do. CMMC was designed to raise the floor — and it does. But nation-state actors aren’t operating at the floor. They’re operating at the ceiling, combining credential theft, OSINT, psychological operations, and mass exfiltration into campaigns that no single compliance checkbox addresses. The defense industrial base needs to stop asking “are we compliant?” and start asking “could we detect what Handala did — and could we survive what comes next when quantum decryption makes every byte they collected readable?” That’s the question CMMC doesn’t answer. That’s the question we’re building QuantaCrypt to address.
Compliance Is Complacency: What the DIB Must Learn from Handala
The defense industrial base is spending billions to achieve CMMC compliance. As of February 2026, roughly 270 of 80,000 contractors have been certified — a 0.3% completion rate with a November 2026 Phase 2 deadline bearing down. The DOJ has already recovered $52 million in cybersecurity-related False Claims Act settlements in FY2025 from contractors who misrepresented their compliance posture.
The rush to compliance is understandable. The danger is treating the certificate as the destination instead of the starting line.
History is clear on this point. Target was PCI-DSS compliant when 40 million credit cards were stolen. Equifax passed multiple compliance audits before 147 million records were breached. FedEx was certified compliant before NotPetya caused $400 million in damage. The pattern isn’t new. Compliance frameworks tell you what to build. They don’t tell you whether what you built actually works against a motivated adversary.
The Lockheed Martin hack is the defense sector’s version of the same lesson. CMMC compliance wouldn’t have detected 375 TB leaving the network. It wouldn’t have caught compromised credentials being used for RDP lateral movement. It wouldn’t have addressed the HNDL exposure that makes every piece of exfiltrated encrypted data a future quantum target.
Compliance is the floor. Security is what you build above it. And in 2026, security for the defense industrial base means post-quantum cryptography, cryptographic asset visibility, and the crypto-agility to adapt as the threat evolves.
The adversary demonstrated their capabilities last week. The question for every defense contractor isn’t whether you’re CMMC compliant. It’s whether you’re actually secure.
Coming soon: We’ve been looking at what it would actually take to detect 375 TB leaving the building — and we think the industry is looking in the wrong place. Stay tuned.
EnQuanta’s QuantaCrypt platform delivers assumption-free, multi-layered encryption built for the defense industrial base. Our dynamic cipher stacks remain durable against unbounded Quantum+AI adversaries — even if one layer is compromised, data remains secure behind others. Start a conversation about what quantum-ready actually looks like →