April 1, 2026
EnQuanta Research Team · 7 min read
Google Quantum AI published a 57-page whitepaper today that should end every remaining debate about whether the quantum threat to cryptography is real, imminent, or theoretical.
It’s none of those things. It’s mathematical. And the math just got 20 times worse.
The paper — co-authored with researchers from the Ethereum Foundation and Stanford University — demonstrates that breaking the elliptic curve cryptography protecting Bitcoin, Ethereum, and virtually every major cryptocurrency requires roughly an order of magnitude fewer quantum resources than previously estimated. Within hours of publication, Bitcoin dropped below $67,000, continuing one of the worst quarters in the asset’s history.
But here’s what the crypto market panic is missing: this paper isn’t about Bitcoin.
It’s about every system on Earth that uses elliptic curve cryptography — and that includes your enterprise TLS certificates, your VPN tunnels, your code-signing infrastructure, and your authentication systems.
The research team compiled two quantum circuits implementing Shor’s algorithm against ECDLP-256 — the elliptic curve discrete logarithm problem that underpins the cryptographic security of Bitcoin, Ethereum, and most modern public-key systems.
Circuit one: fewer than 1,200 logical qubits and 90 million Toffoli gates. Circuit two: fewer than 1,450 logical qubits and 70 million Toffoli gates.
In physical qubit terms, this translates to fewer than 500,000 physical qubits needed to break ECDLP-256. Previous estimates put this number in the millions. That’s a 20-fold reduction in the hardware required to break one of the most widely deployed cryptographic standards on the planet.
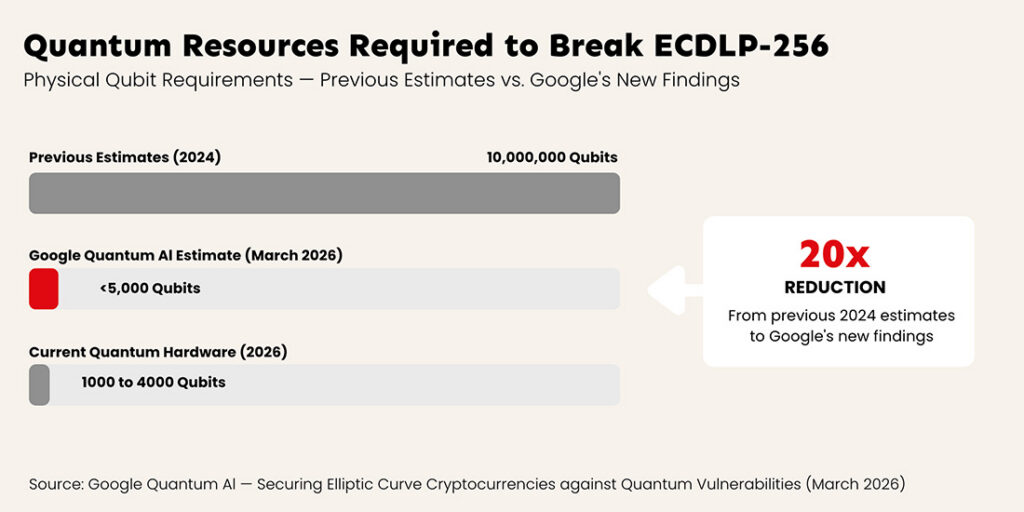
To put this in context: IBM’s quantum roadmap targets systems exceeding 100,000 qubits within the next several years. Google’s own Willow chip demonstrated exponential error reduction as qubit counts scale. The gap between current hardware and the hardware needed to execute these attacks is no longer measured in orders of magnitude — it’s measured in engineering generations.
The paper models a live attack where a quantum adversary intercepts an in-flight Bitcoin transaction. When you send Bitcoin, your public key is briefly exposed during the transaction broadcast. A sufficiently powerful quantum computer could extract the private key from that public key in approximately nine minutes — giving it a 41% chance of beating Bitcoin’s 10-minute block confirmation time.
That’s not a theoretical attack path. That’s a race condition with quantifiable odds.
The researchers estimate that 6.9 million Bitcoin with already-exposed public keys are at immediate risk when quantum hardware reaches sufficient scale. For Ethereum, the paper identifies five distinct quantum attack paths that could put more than $100 billion in assets at risk.
Here’s the detail that should alarm security professionals far more than the qubit numbers: Google chose not to publish the actual quantum circuits.
Instead, the research team used a zero-knowledge proof to validate their results — allowing independent researchers to verify the resource estimates without revealing the specific techniques needed to reproduce the attack. This approach was developed in coordination with the US government.
Read that again. Google treated their own research paper like a vulnerability disclosure. They used responsible disclosure practices — the same framework used for software zero-days — because they consider the results sensitive enough that publishing the full methodology could accelerate adversary capability.
When the company with the world’s most advanced quantum computing program handles their own cryptographic research like a CVE, that tells you everything about where the threat timeline actually stands.
Our Take: The responsible disclosure angle is the real story here. Google has published hundreds of quantum computing papers over the years. They publish circuit designs, error correction results, and performance benchmarks openly. But this paper? They withheld the circuits and coordinated with the US government before release. That’s not how you handle theoretical research. That’s how you handle an active vulnerability in critical infrastructure — which is exactly what elliptic curve cryptography is.
The market is treating this as a Bitcoin problem. It’s not. ECDLP-256 doesn’t just protect cryptocurrency wallets. It protects:
TLS/SSL certificates — The encryption protecting virtually every web connection, API call, and cloud service communication. If ECDLP-256 falls, so does the trust model underpinning the internet’s transport security.
Code-signing infrastructure — The digital signatures that verify software updates are authentic. A quantum adversary that can forge ECDSA signatures can push malicious updates that appear to come from legitimate vendors.
Authentication systems — FIDO2/WebAuthn security keys, SSH keys, certificate-based VPN authentication — all built on elliptic curve cryptography. Breaking ECC doesn’t just expose data. It enables impersonation at every level of the identity stack.
IoT and embedded devices — Billions of devices using ECC for firmware verification and secure communication, many of which cannot be updated and will remain in service for decades.
The Bitcoin price drop is the visible symptom. The underlying condition is that a foundational cryptographic primitive is approaching its expiration date, and most enterprises haven’t started planning the transition.
Our Take: CISOs who dismissed the quantum threat because “we don’t hold Bitcoin” need to revisit that assumption today. Your organization almost certainly depends on ECDLP-256 in places you haven’t inventoried — embedded in hardware security modules, baked into IoT device firmware, hardcoded in legacy authentication flows. Google just demonstrated the resources needed to break these systems are 20x smaller than the industry assumed last year. The question isn’t whether ECC will be broken. It’s whether you’ll have migrated before it is.
Zoom out from the technical findings and look at what Google did this week in aggregate:
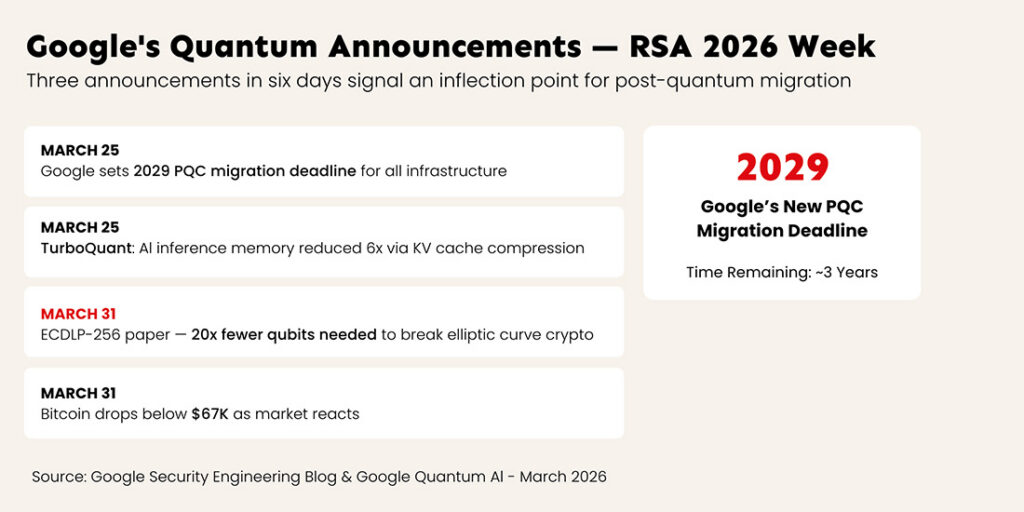
On March 25, Google announced a 2029 deadline for migrating all of their infrastructure to post-quantum cryptography — prioritizing authentication and digital signatures.
On March 25, Google Research published TurboQuant, making AI inference 6x more memory-efficient — accelerating the AI side of the Quantum+AI threat convergence.
On March 31, Google published a paper demonstrating that breaking ECC requires 20x fewer qubits than previously thought — and handled it like a vulnerability disclosure.
This is the same company, in the same week, telling you three things: quantum is closer than you think, AI is making attacks cheaper, and the cryptographic math that protects your infrastructure is weaker than assumed.
When a company with this much visibility into both quantum hardware and AI capability sets a 2029 migration deadline and simultaneously publishes a paper showing ECC is more vulnerable than estimated — they’re not theorizing. They’re preparing. The question is whether you are too.
Google’s cryptocurrency whitepaper will be remembered as the moment the quantum threat stopped being abstract and became measurable. Not because the threat is new — harvest-now-decrypt-later attacks have been underway for years. But because the resource estimates just collapsed by an order of magnitude, and the organization responsible for some of the world’s most advanced quantum hardware chose to handle its own findings like a national security disclosure.
For the cryptocurrency community: the migration to quantum-resistant signatures is no longer optional. The paper’s authors — including researchers from the Ethereum Foundation — are telling you the runway is shorter than assumed.
For enterprise security teams: if you’re still treating post-quantum cryptography as a 2030 problem, this paper just moved your deadline. Every system in your environment that depends on elliptic curve cryptography — TLS, code signing, authentication, IoT — now has a shorter shelf life than your last risk assessment assumed.
For everyone: Google set a 2029 PQC migration deadline for themselves this week. They just published a paper proving why. The clock isn’t theoretical anymore. It’s ticking, and today we learned it’s ticking faster than anyone calculated.
EnQuanta’s Dynamic-Hybrid Crypto-Agile Framework exists because the timeline for quantum threats keeps compressing — and organizations need cryptographic infrastructure that can adapt without waiting for the next paper to tell them they’re already behind. Crypto-agility isn’t about picking the right algorithm today. It’s about building the architecture that lets you change algorithms tomorrow, without stopping operations. Learn how our framework lets you swap algorithms without downtime →