At EnQuanta, we understand the critical security demands of government agencies. With a proven track record in safeguarding national security assets, we meet and exceed federal standards like FISMA and FedRAMP. Our solutions are trusted by defense, intelligence, and governmental bodies, providing unmatched security for mission-critical data.
Technologies tested and piloted in collaboration with the NSA and CISA-designated National Center of Academic Excellence in Cyber Defense.
Tested and deployed in U.S. Military programs, including providing anti-tamper security for frontline weapon systems.
Secrecy Orders requested by the National Security Agency (NSA) and the Office of Naval Research (ONR) were lifted in 2Q2025.
Auto-hybrid crypto-agile technology evaluated under ITAR (International Traffic in Arms – State Dept) and EAR (Export Article Restrictions – Commerce Dept) for compliance.
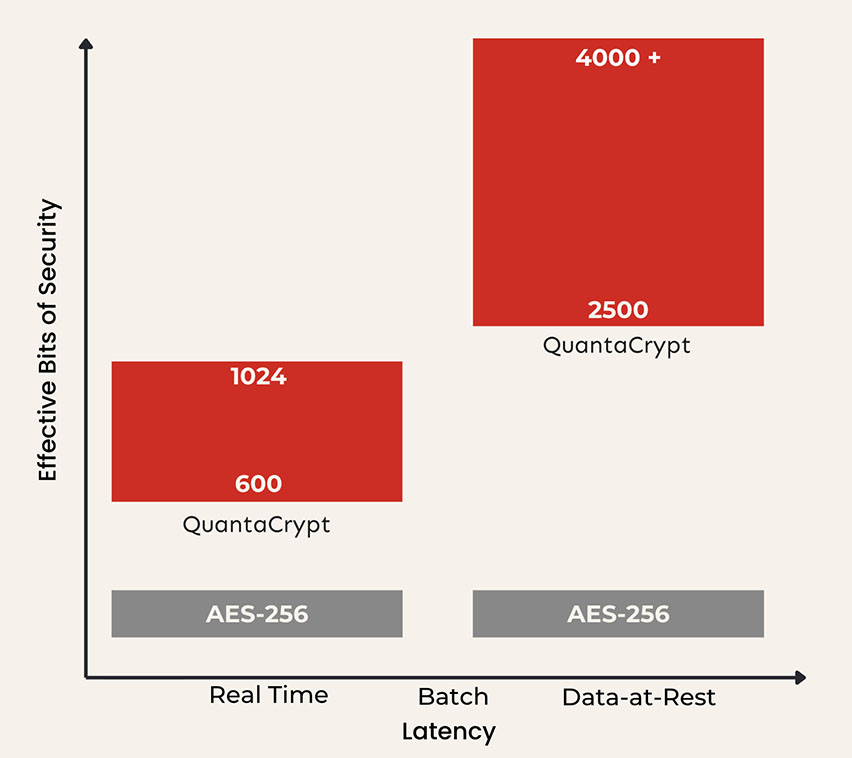
QuantaCrypt surpasses AES-256 with exponentially more complex protection, delivering security levels exceeding a googol-scale (1 followed by 100 zeros) beyond AES-256. Its integrated hybrid key establishment generates unique, non-reusable stacked ciphers and keys for each protected data chunk. Managed crypto-agility supports both NIST-standard and patented ciphers to sustain Quantum+AI cyber resilience as requirements evolve.
Designed for ease of deployment and quick integration into existing security architecture. No hardware replacement or software refactoring of applications, storage, and network infrastructure needed.
Integrate assumption-free cryptography into custom and commercial applications with simple to use APIs, services, and communication libraries providing Post Quantum+AI protection for large data sets, real-time communication, and safe data transfer over unsecure channels.
Defend mission-critical data with RAID-10 Network storage solution delivering fault tolerant, and anti-ransomware PQC security greater than NIST standards. Compatible with heterogeneous network environments installable on bare metal, virtualized, edge, and cloud infrastructure. Supports Distribute, Retrieve, Purge operations for integration with simple API calls.
Quantum harden digital assets that contain intellectual property, and data-sets from tampering and reverse engineering. Integrates with existing key management and utilizes software-only, air-gapped, NIST-certified QRNG. Designed for SW/HW engineers deploying data to write-once, read-many scenarios such as field deployed assets and IoT devices.

Challenge: There is a need to protect fire control software and embedded sensor firmware on frontline laser weapon systems from tampering or reverse-engineering if captured. The solution had to preserve the integrity of an exposed high-value asset over decades.
Solution: EnQuanta deployed QuantaCrypt Vault, our software anti-tamper solution. Using our crypto-agile approach, Vault secures firmware and embedded software against current and future quantum-level threats.
Outcome: The weapon system’s operational software is protected, supporting mission readiness and safeguarding critical defense technology from compromise.
Download our capabilities statement, a one-page document that outlines our core competencies, unique differentiators, and essential company data (CAGE code, NAICS codes).
As you begin to evaluate risks and options, we can support your process with deep insight and guidance. Contact us to explore your questions, your priorities, and next steps.