
April 3, 2026
EnQuanta Research Team · 7 min read
Three days after RSA Conference ended — where the FBI’s Cyber Division Assistant Director stood on stage at the NightDragon Innovation Summit discussing escalating nation-state threats — an Iran-linked hacking group demonstrated exactly what he was talking about.
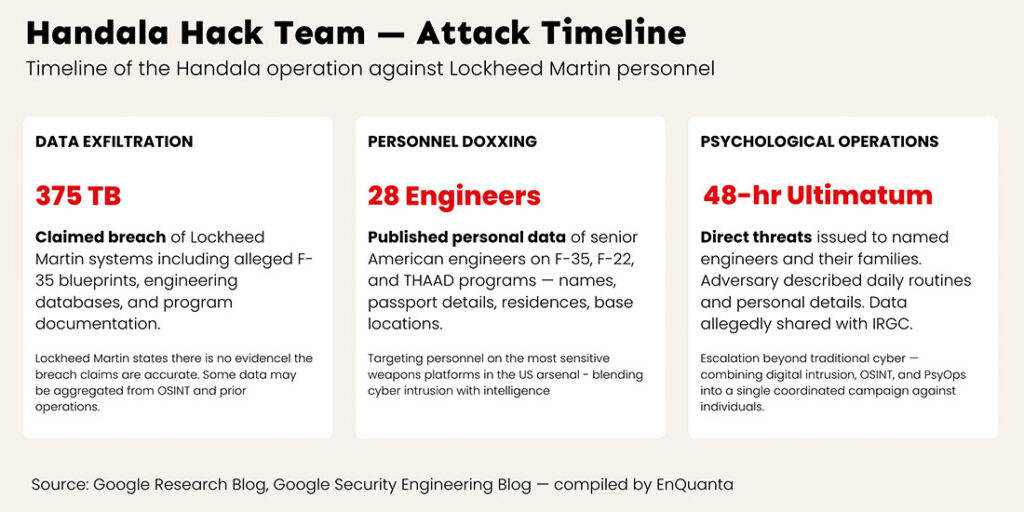
Handala Hack Team claimed to have breached Lockheed Martin‘s defenses and published the personal and professional data of 28 senior American engineers working on some of the most sensitive weapons platforms in the US arsenal. Then they issued threats to the engineers’ families.
This isn’t a ransomware story. It’s an intelligence operation with a psychological warfare component — and it’s a preview of what the harvest-now-decrypt-later threat looks like when adversaries don’t even need quantum computers to weaponize what they’ve already collected.
Inside the Lockheed Martin Hack: 375 TB and 28 Targeted Engineers
During the final days of RSA Conference week, Handala — a group that multiple cybersecurity firms and US authorities have linked to Iran’s Ministry of Intelligence (MOIS) — announced what it called “a new phase of Operation Lockheed Martin.”
The group claimed to have exfiltrated up to 375 terabytes of data from Lockheed Martin, allegedly including blueprints for the F-35 stealth fighter. While Lockheed Martin has stated there is no evidence the breach claims are accurate and has reaffirmed confidence in their cybersecurity, what happened next is independently verifiable and deeply concerning.
Handala published the personal data of 28 senior American engineers working on Israeli military projects — including maintenance of F-35 and F-22 fighter jets and the THAAD missile defense system. The leaked data included names, identification numbers, passport details, places of residence, and service base locations.
The operation then escalated beyond a traditional data breach:
The named engineers received a 48-hour ultimatum to leave Israel. Handala contacted some engineers directly, describing their daily routines, their favorite restaurants, and details about their families. The threats extended to relatives in the United States. The group claimed the stolen data had been shared with the IRGC.
This is targeting at a level that blends cyber intrusion, open-source intelligence aggregation, and psychological operations into a single campaign — aimed at the individuals who maintain the most advanced weapons systems in the Western arsenal.
OSINT and Nation-State Cyber Espionage: The Amplification Problem
Cybersecurity experts analyzing the Handala campaign have noted that much of the doxxed information may have been gathered through a combination of open-source intelligence (OSINT) and data from previous espionage operations, not necessarily a direct network breach. This doesn’t make it less dangerous — it makes it more dangerous.
It means nation-state adversaries are aggregating data from multiple sources — social media profiles, public records, previously leaked databases, compromised personal accounts, and potentially intercepted communications — to build targeting profiles of defense sector personnel. Each individual data source might seem harmless. Combined, they become an operational intelligence product.
This is the OSINT amplification problem that the defense industrial base hasn’t adequately addressed: the explosion of personal data across commercial platforms, combined with nation-state resources for aggregation and analysis, means that individual engineers working on classified programs can be identified, located, profiled, and threatened without ever directly breaching a classified network.
This attack didn’t happen in a vacuum. At the NightDragon Innovation Summit just days earlier, the panels on “The Next Threat Cycle” and “AI in Action: The Battlefield is Now Digital” made the same point from the defender’s perspective: AI-driven operations, nation-state escalation, and the convergence of cyber and physical threats are creating an attack surface that traditional perimeter security can’t contain.
The Lockheed hack is a case study in exactly that convergence. The adversary combined cyber intrusion (or claims of it), OSINT aggregation, direct personal contact with targets, and public psychological pressure into a single coordinated campaign. The digital and physical threat boundaries didn’t just blur — they disappeared.
Our Take: The defense industrial base needs to stop treating personal data security and classified network security as separate problems. Handala didn’t need to breach Lockheed’s classified networks to create a national security incident. They targeted the people — and in doing so, demonstrated that human targeting can be just as operationally effective as network penetration. When an adversary can describe an engineer’s daily routine and threaten their family, the security perimeter has already been breached in the ways that matter most.
Now layer in the dimension that transforms this from a current incident into a long-term strategic threat.
Every encrypted communication between these 28 engineers and Lockheed Martin — every VPN session, every email containing technical specifications, every video call discussing program details — any of it transmitted using RSA or elliptic curve cryptography (ECC) is potentially sitting in adversary storage.
This isn’t speculation. Multiple intelligence agencies have confirmed that nation-state adversaries are conducting harvest-now-decrypt-later operations at an industrial scale. Iran, China, and Russia have all been identified as actively exfiltrating encrypted data from defense, intelligence, and critical infrastructure targets.
The timeline matters here. Google published a whitepaper this week demonstrating that breaking elliptic curve cryptography requires 20x fewer quantum resources than previously estimated — fewer than 500,000 physical qubits. Google simultaneously announced a 2029 PQC migration deadline for their own infrastructure.
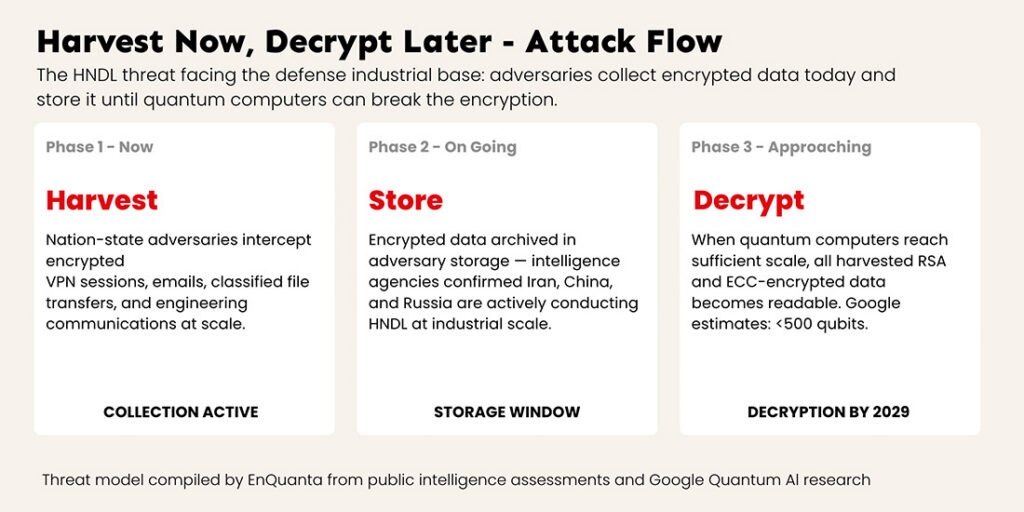
Connect the dots: If Iran-linked actors are building operational profiles of engineers on F-35 and THAAD programs today using data they can already read, imagine what they’ll be able to do when they can decrypt the classified and sensitive communications those same engineers have been sending for the past decade.
The Handala operation demonstrates that the collection phase is well underway. Google’s research tells us the decryption phase may arrive sooner than assumed. The gap between collection and decryption is the window the defense industrial base has to migrate to post-quantum cryptography — and that window just got shorter.
Our Take: The Lockheed Martin hack is what the harvest-now-decrypt-later threat looks like in practice — except the adversary didn’t even need to wait for quantum decryption to cause damage. The defense sector is the canary in the quantum coal mine. If Iran-linked actors are already this aggressive with the data they can access through classical means, the strategic value of their encrypted data archives only grows as quantum decryption becomes feasible. The defense sector’s PQC migration isn’t a compliance checkbox — it’s a national security imperative, and the adversary timeline is running ahead of the defender timeline.
Map your cryptographic exposure surface. Not just your classified networks — your personnel data, your engineering communications, your VPN configurations, your supply chain partner integrations. The Handala operation targeted people, not systems. Your Cryptographic Bill of Materials needs to include every channel through which sensitive personnel data and program information flows.
Assess your HNDL exposure window. For every encrypted data store and communication channel, calculate the sensitivity window: how long does this data remain valuable? For defense programs with multi-decade lifecycles, the answer is often “longer than the time until quantum decryption arrives.” That data needs post-quantum cryptography protection now, not when a mandate forces it.
Extend your security perimeter to personal accounts. The Handala campaign exploited personal data and personal communications — not enterprise systems. Defense contractors need to provide security guidance, monitoring tools, and incident response coverage that extends to the personal digital lives of employees working on sensitive programs.
Require PQC readiness from your supply chain. Lockheed Martin operates within a vast ecosystem of subcontractors, technology vendors, and partner organizations. Every communication channel between partners is a potential harvest-now-decrypt-later collection point. Quantum-readiness audits of your partner ecosystem should start immediately.
The Lockheed Martin hack happened during RSA week — a coincidence of timing that couldn’t be more fitting. While the cybersecurity industry gathered in San Francisco to discuss the escalating threat landscape, a nation-state adversary provided a real-time demonstration of exactly what those panels were warning about.
The defense industrial base sits at the intersection of every quantum threat vector: it holds data with multi-decade sensitivity windows, it’s actively targeted by nation-state adversaries conducting harvest-now-decrypt-later operations, and its personnel are individually valuable enough to be targeted with combined cyber-physical campaigns.
Google’s research this week showed that the quantum timeline is compressing. The Handala operation showed that the adversary isn’t waiting. The RSA conversations showed that the industry knows what needs to happen. The only remaining question is execution speed — and for the defense sector, the margin for delay just disappeared.
EnQuanta’s Dynamic-Hybrid Crypto-Agile Framework was designed for exactly this threat environment — where adversaries are already collecting, timelines are compressing, and organizations need cryptographic infrastructure that can adapt faster than the threat evolves. For the defense industrial base, crypto-agility isn’t a technology choice. It’s a strategic necessity.
Learn how our framework protects against the HNDL threat →