April 2, 2026
Tucker Saxon · 8 min read
We just got back from RSA Conference 2026 in San Francisco, and the shift was unmistakable. Post-quantum cryptography and crypto-agility weren’t side conversations this year. They were the conversation — and for the first time, they were discussed as two halves of the same imperative.
Two years ago, PQC panels were corner-booth affairs, sandwiched between zero-trust demos and cloud security keynotes. This year, both the threat and the architectural response were everywhere — on the main stage, in the hallway conversations, and embedded in the product roadmaps of companies that had never mentioned quantum before. PQC defined what needs to change. Crypto-agility defined how organizations can actually get there without ripping out their infrastructure. The tone didn’t just shift incrementally. It shifted fundamentally.
And then, as if to validate every urgent conversation we heard on the show floor, Google dropped two bombshells during the conference itself.
Two events crystallized where the industry stands.
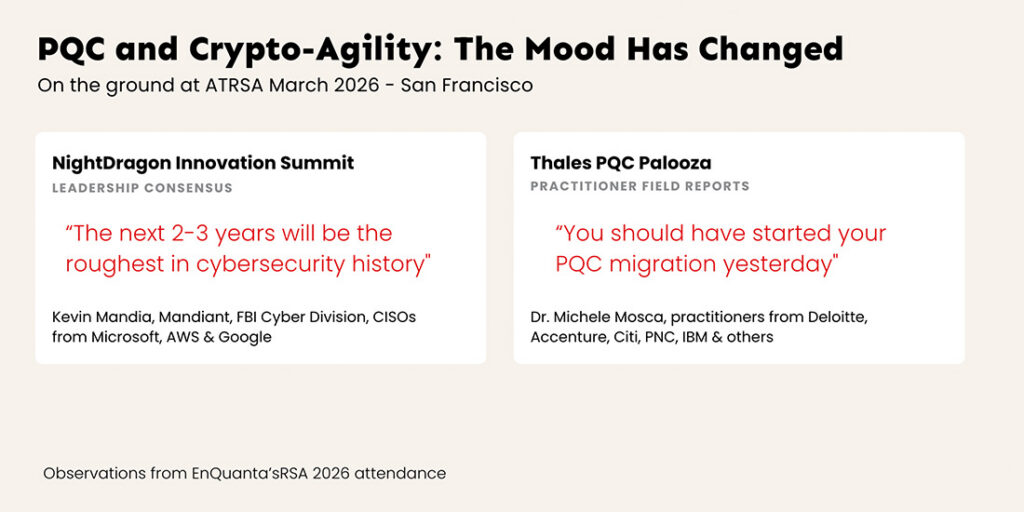
At the NightDragon Innovation Summit, some of the most influential leaders in cybersecurity delivered a blunt assessment of the threat landscape. Kevin Mandia, Google Cloud’s Mandiant CTO Charles Carmakal, the FBI’s Cyber Division Assistant Director Brett Leatherman, and CISOs from Microsoft, AWS, and Google shared a stage — and shared a message that was impossible to misread.
The consensus: the next two to three years will be rough. Not because of any single threat vector, but because of convergence. AI-powered offensive operations, nation-state escalation, and the approaching quantum horizon are hitting simultaneously. The panel on “The Next Threat Cycle” laid it out plainly — from nation-state behavior to AI-driven operations to cyber-physical risk, the attack surface is expanding on every axis at once.
The message across the Summit was consistent: shore up defenses now, be as proactive as possible, and stop treating the quantum threat as tomorrow’s problem. The implication was clear — when threat vectors are converging this fast, static cryptographic infrastructure becomes a liability. You need the ability to adapt your cryptography as the threat evolves.
If NightDragon painted the threat picture, the Thales PQC Palooza got into the operational details. Dr. Michele Mosca— one of the foremost authorities on quantum cryptographic risk — opened with a demonstration of where PQC stands today and laid out the critical next steps organizations need to take to reach a quantum-safe cryptographic posture.
What followed was hours of panel discussions featuring practitioners from Deloitte, Accenture, Citi, PNC, IBM, and others. These weren’t theoretical presentations. They were field reports from organizations that have started the migration — lessons learned, integration challenges, performance considerations, and the compliance landscape shaping timelines. A recurring theme: organizations that built crypto-agile architectures early are migrating faster and with less disruption than those attempting a single monolithic algorithm swap.
The takeaway was unanimous and unequivocal: everyone needs to start their PQC transitions yesterday — and the organizations doing it well are the ones that invested in crypto-agility first.
Our Take: RSA is a barometer for where the industry’s collective attention sits, and this year the needle moved decisively toward both post-quantum readiness and the crypto-agile architectures needed to achieve it. The conversations we had — with CISOs, government leaders, and security architects — weren’t about whether PQC migration matters. They were about how to execute it without breaking everything in production. The answer that kept surfacing: crypto-agility — the ability to swap, layer, and manage cryptographic algorithms dynamically as standards evolve and threats escalate. When the practitioners who are actually doing the migration work say “you should have started yesterday,” the planning phase is over.
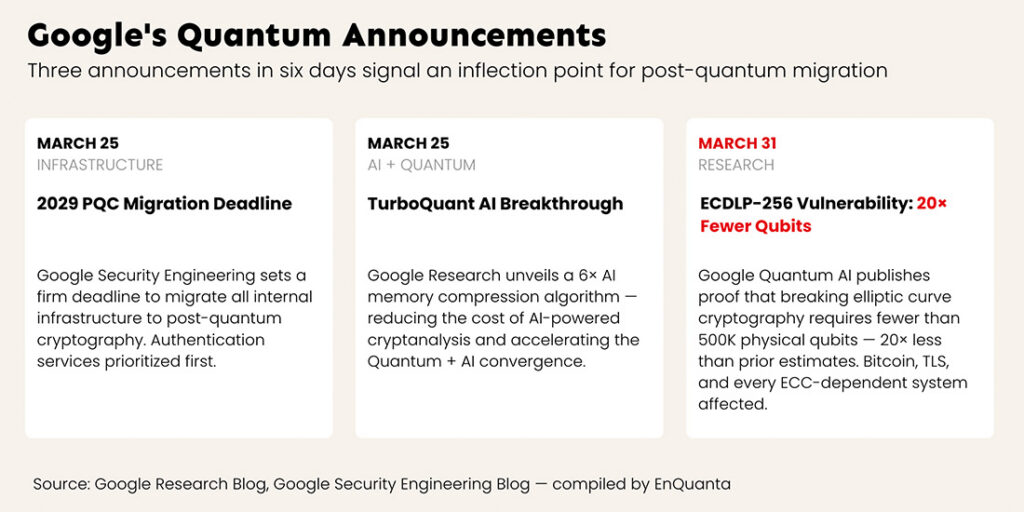
Google’s 2029 Post-Quantum Cryptography Deadline: Why Every Enterprise Should Pay Attention
On March 25 — the same day as the Thales PQC Palooza — Google’s Security Engineering team published a timeline for migrating all of Google’s infrastructure to post-quantum cryptography by 2029.
The announcement came from Heather Adkins, VP of Security Engineering, and Sophie Schmieg, Senior Staff Cryptography Engineer. This is Google’s security infrastructure leadership — not marketing, not a blog from the AI hype cycle — drawing a line in the sand.
The announcement makes three things explicit:
Authentication is the priority. Google has adjusted its internal threat model to prioritize PQC migration for authentication services — digital signatures, not just encryption. This is a significant shift. Most enterprise PQC conversations focus on protecting data at rest and in transit. Google is telling you that identity verification is the urgent battlefront. If a quantum computer can forge digital signatures, it doesn’t need to decrypt your data — it can impersonate your systems, your certificates, and your users.
Consumer deployment is happening now. Android 17 is integrating PQC digital signature protection using ML-DSA, one of NIST’s standardized post-quantum algorithms. Google considers the threat imminent enough to deploy PQC at consumer scale — into the hands of billions of device users — not just in enterprise or government environments.
The 2029 deadline is derived from internal intelligence. Google doesn’t set aggressive migration timelines for theoretical risks. They operate one of the world’s most advanced quantum computing programs. They have more visibility into quantum hardware progress than virtually any other organization on the planet. When they say 2029, they’re translating their own R&D roadmap into a compliance calendar.
Our Take: At RSA, we heard CISOs from every sector asking the same question: “How much time do we actually have?” Google just answered. They build the quantum computers. They build the AI systems. They run one of the largest cryptographic infrastructures on Earth. If Google’s internal threat model says authentication services need PQC by 2029, your threat model should too. And here’s the critical detail: Google isn’t migrating to a single algorithm. They’re building crypto-agile infrastructure that can adapt as standards evolve — because even they know today’s PQC algorithms may not be the final answer. The enterprises that treat Google’s timeline as a ceiling rather than a floor are the ones that will get caught in the gap between preparation and necessity.
TurboQuant and the AI-Quantum Threat Convergence: What CISOs Are Missing
The same day Google published its PQC timeline, Google Research unveiled TurboQuant — a novel AI memory compression algorithm that reduces the KV cache (the working memory AI models use during inference) by at least 6x without meaningful quality loss. The method uses vector quantization via two new techniques: PolarQuant for the compression itself and QJL for training optimization, with findings to be presented at ICLR 2026.
The tech press covered TurboQuant as an AI efficiency story. The internet compared it to Pied Piper from HBO’s Silicon Valley. Cloudflare’s CEO called it “Google’s DeepSeek moment.” What nobody connected is what TurboQuant means for the Quantum+AI threat convergence — exactly the convergence that NightDragon panelists spent an entire afternoon warning about.
Here’s the connection most analysts are missing: AI-assisted cryptanalysis is computationally expensive. Running AI models that identify patterns in encrypted traffic, optimize quantum attack parameters, or reduce the search space for brute-force operations requires massive amounts of inference compute. TurboQuant doesn’t just make chatbots cheaper to run — it makes every AI-powered attack vector more accessible and more scalable.
A 6x reduction in inference memory means AI-assisted cryptanalytic attacks that previously required state-level GPU clusters can potentially run on substantially smaller hardware. It means adversaries can run more attack iterations in the same time window. It means the economic barrier to deploying AI as a force multiplier for quantum and classical cryptographic attacks just dropped significantly.
Our Take: The Quantum+AI convergence isn’t a theoretical framework — it’s accelerating on both axes simultaneously. Quantum hardware is advancing. AI efficiency is compounding. Each advancement multiplies the other. This is exactly why crypto-agility matters as much as PQC itself: when the threat landscape shifts this fast, any cryptographic architecture that requires a full replacement cycle every time a new attack vector emerges is already obsolete by the time it’s deployed. CISOs who track quantum timelines but ignore AI efficiency breakthroughs are watching one hand while the other picks their pocket. The NightDragon panelists were right: the threat landscape over the next two to three years isn’t about quantum or AI. It’s about what happens when they converge — and TurboQuant just accelerated that convergence.
RSA 2026 was the conference where two things became inseparable: the urgency of post-quantum cryptography migration and the necessity of crypto-agile architecture to execute it. The hallway conversations matched the keynote urgency. The vendor demos included PQC integration. And the practitioners who’ve started migrating told everyone else that the inventory phase is over — the migration phase has begun.
Then Google validated every urgent word spoken at the conference by setting a 2029 deadline and deploying PQC in Android 17 on the same day.
If Google needs three years to complete their migration — starting now, with full executive commitment and some of the deepest cryptographic expertise on the planet — ask yourself: how long will your migration take, and when did you start?
The enterprises still in the planning phase are already behind. The ones that haven’t started are operating on borrowed time that’s accruing interest in an adversary’s data archive. And the ones attempting PQC migration without crypto-agile infrastructure are building a solution that’s brittle before it’s finished — because the threat landscape will shift again before their deployment is complete. RSA 2026 made that clear. Google made it undeniable.
EnQuanta’s Dynamic-Hybrid Crypto-Agile Framework was built for exactly this moment — when the migration timeline compresses faster than traditional infrastructure modernization can handle. Crypto-agility isn’t a feature. It’s the architecture that lets you adapt as the threat evolves, without ripping out your infrastructure every time a new algorithm is standardized or a new attack vector emerges.
Learn how our framework lets you migrate without ripping out your infrastructure →