
April 17, 2026
EnQuanta Research Team · 7 min read
Last week, twelve of the most powerful technology companies on earth — Amazon, Apple, Google, Microsoft, NVIDIA, CrowdStrike, Cisco, Broadcom, Palo Alto Networks, JPMorganChase, the Linux Foundation, and Anthropic — formed an emergency coalition called Project Glasswing. Over 40 additional organizations quietly joined them.
The reason: an AI model called Claude Mythos Preview had found thousands of zero-day vulnerabilities — many of them critical — in every major operating system, every major web browser, and the cryptographic libraries that the entire internet relies on.
Read that again. Not a few vulnerabilities in niche software. Thousands of unknown flaws across the foundations of digital infrastructure, including bugs in TLS, AES-GCM, and SSH implementations that could allow certificate forgery or decryption of encrypted communications. One vulnerability had survived 27 years of human review. Another, 16 years. Automated testing tools had scanned these codebases millions of times without finding them.
When Apple, Google, and Microsoft form a joint defensive coalition and Anthropic commits $100 million in resources to the effort, the threat isn’t theoretical. It’s here.
And for the defense industrial base — already reeling from the Lockheed Martin hack — this changes the threat model fundamentally.
For roughly two decades, the cybersecurity landscape operated on an implicit equilibrium: skilled human attackers versus skilled human defenders, with tooling advantages shifting back and forth. Vulnerability discovery was labor-intensive. Exploitation required expertise. The best human security researchers could find perhaps dozens of critical vulnerabilities per year in major software.
Mythos Preview shattered that equilibrium in weeks.
Anthropic’s own assessment is blunt: AI models have reached a capability level where they surpass all but the most skilled humans at finding and exploiting software vulnerabilities. The model didn’t just find known vulnerability patterns faster — it found classes of bugs that decades of human review, fuzzing, and automated analysis had missed entirely.
The implications for cryptography are immediate and specific.
Implementation vulnerabilities in battle-tested crypto libraries. Mythos found flaws in TLS, AES-GCM, and SSH — protocols and algorithms that have had years to decades of scrutiny from the world’s best cryptographers. These aren’t theoretical weaknesses in the mathematical foundations of the algorithms. These are implementation bugs — the kind that let an attacker forge certificates or decrypt communications without ever breaking the underlying math.
No single implementation is safe when AI can probe faster than humans can review. The lesson from Mythos isn’t that older code is safer or newer code is riskier. It’s that any single cryptographic implementation — regardless of maturity — now faces an adversary that can find flaws at machine speed. NIST’s post-quantum cryptography standards (FIPS 203, 204, 205) represent the next generation of cryptographic defense. But the Mythos findings demonstrate that no single algorithm, classical or post-quantum, should be trusted as the sole layer of protection. The answer isn’t picking the “right” algorithm — it’s building architectures where no single implementation failure compromises the system.
Project Glasswing addresses the AI side of the equation. But Glasswing’s coalition members are simultaneously dealing with a second, converging threat.
Google opened early access to its Willow quantum processor in March 2026 — the same chip that performed a computation in under five minutes that would take a classical supercomputer 10 septillion years. Google has set a 2029 PQC migration deadline for its own infrastructure. NSA’s CNSA 2.0 mandates quantum-resistant cryptography for National Security Systems by January 2027.
Here’s the convergence that should alarm every defense CISO:
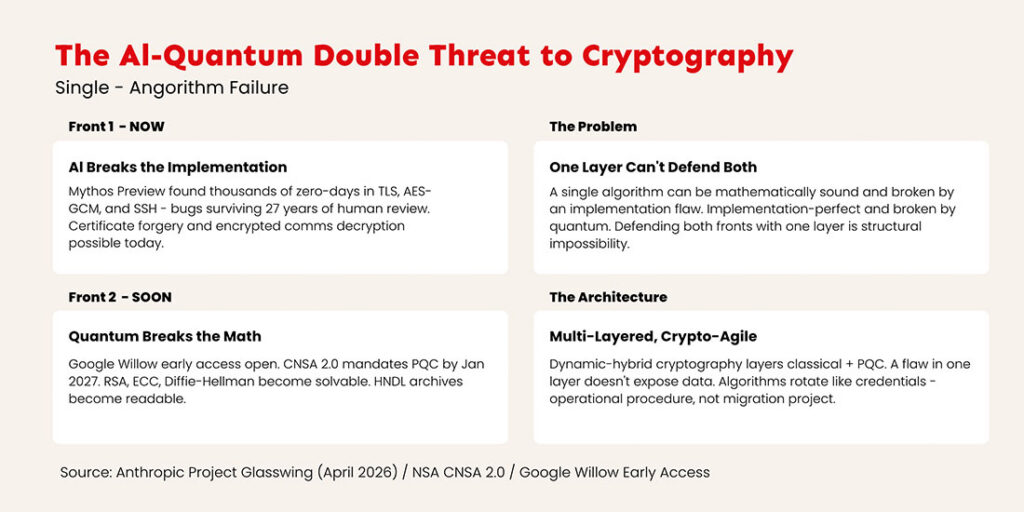
AI breaks the implementation. Mythos demonstrated that the way cryptographic algorithms are coded — in the libraries, protocols, and software stacks that every organization depends on — contains exploitable flaws. Today. Not in theory. Not on a research timeline. Today.
Quantum breaks the math. When fault-tolerant quantum computers arrive at scale, the mathematical foundations of RSA, ECC, and classical Diffie-Hellman become solvable. The harvest-now-decrypt-later operations we’ve been warning about — and that the Lockheed Martin hack demonstrated — become decrypt-now operations.
These threats compound. An adversary with AI-assisted vulnerability discovery and quantum decryption capability doesn’t need to choose between attacking the implementation and attacking the algorithm. They attack both. They find the implementation flaw with AI today, exfiltrate the data, and decrypt whatever they couldn’t read immediately once quantum catches up. Two attack surfaces. One target. Zero redundancy in a single-algorithm defense.
This is the core problem Glasswing’s formation exposes. The cybersecurity industry has spent decades building defense around individual algorithms and their implementations: RSA for key exchange, AES for symmetric encryption, SHA for hashing. Each one a single point of failure.
When the only threat was mathematical — “can someone factor large primes fast enough?” — a single algorithm with sufficient key length was defensible. The attack surface was narrow: break the math or don’t.
Mythos just proved the attack surface is much wider than the math. It includes every line of code that implements that math, every protocol that wraps it, and every library that ships it. Thousands of bugs across millions of lines of code that human reviewers missed for decades.
A single algorithm can be mathematically sound and still be broken by an implementation flaw. A single algorithm can be implementation-perfect today and still be broken by a quantum computer tomorrow. Defending both fronts simultaneously with one layer of cryptography is a structural impossibility.
This is the architectural argument for multi-layered, crypto-agile defense — and it just went from theoretical to urgent.
QuantaCrypt’s approach was designed for exactly this convergence — though we’ll admit, we didn’t expect AI to prove the point this dramatically.
Dynamic-hybrid cryptography. QuantaCrypt doesn’t rely on a single algorithm. It layers multiple cryptographic approaches — classical and post-quantum — so that a vulnerability in any one layer doesn’t expose the data. If Mythos (or its successors) finds a flaw in one algorithm’s implementation, the remaining layers maintain protection. If a quantum computer breaks the classical math, the PQC layers hold. No single point of failure.
Crypto-agility by design. When Anthropic finds implementation flaws in a crypto library — and they will keep finding them — organizations need the ability to swap algorithms without rearchitecting their infrastructure. QuantaCrypt’s framework lets you rotate cryptographic primitives the way you rotate credentials: as an operational procedure, not a multi-year migration project.
Assumption-free architecture. The lesson of Mythos is that assumptions kill. The assumption that 27 years of human review meant code was secure. The assumption that AES-GCM implementations were bulletproof. The assumption that you had years before AI-assisted attacks became real. QuantaCrypt is built on zero assumptions about which algorithms will remain secure — because in 2026, that assumption is no longer safe.
Our Take: Glasswing is the biggest signal the tech industry has ever sent about the state of software security — and most people are reading it wrong. The headline is “AI finds bugs.” The real story is that the twenty-year equilibrium between offense and defense just broke. AI gave offense a permanent structural advantage in vulnerability discovery. Quantum is about to give offense a permanent structural advantage in cryptanalysis. Organizations that are still defending with single-algorithm cryptography on both fronts are bringing a shield to a fight where the adversary just got two new weapons. The defense industrial base — already targeted by Handala, already exposed by CMMC’s gaps, already hemorrhaging data to harvest-now-decrypt-later operations — cannot afford to wait for the next Mythos disclosure or the next quantum milestone to act. The convergence is here. The architecture has to change.
The Glasswing coalition will patch the specific vulnerabilities Mythos found. That’s necessary. It’s not sufficient.
Audit your cryptographic dependencies now. If Mythos found implementation flaws in the most widely scrutinized crypto libraries in the world, what’s lurking in your organization’s custom implementations, vendor-specific libraries, and legacy systems? A cryptographic bill of materials isn’t optional anymore — it’s the starting point for understanding your exposure to both AI-discovered and quantum-enabled attacks.
Migrate to post-quantum cryptography on an accelerated timeline. Google set 2029 as their deadline. NSA’s CNSA 2.0 requires quantum-resistant algorithms for National Security Systems by January 2027. The Mythos disclosure just compressed the urgency — because AI-assisted attackers don’t need to wait for quantum to exploit the implementation flaws in your classical crypto.
Build for crypto-agility, not crypto-migration. Every vulnerability Mythos finds, every PQC standard NIST updates, every quantum milestone Google announces — each one potentially requires a cryptographic response. Organizations that build for a single algorithm swap will face the same scramble repeatedly. Crypto-agility is the ability to adapt to any of these events as an operational procedure, not an emergency.
Assume your current cryptography has undiscovered flaws. Mythos proved this is a statistical certainty, not paranoia. Multi-layered encryption ensures that undiscovered vulnerabilities in any single layer don’t compromise the entire defense.
The adversary landscape shifted permanently this week. AI and quantum aren’t future threats converging on a distant horizon. One is here. The other is closer than the industry admits. The organizations that survive both are the ones building layered, agile defenses today — not the ones waiting for the next disclosure to react.
EnQuanta’s QuantaCrypt platform delivers assumption-free, multi-layered encryption built for the defense industrial base. Our dynamic cipher stacks remain durable against unbounded Quantum+AI adversaries — even if one layer is compromised, data remains secure behind others. Start a conversation about what quantum-ready actually looks like →